As a provider of critical infrastructure and one of Australia's largest phone companies, the question on everyone's lips is, "how was Optus hacked"? And for those who fell victim to it, "what does it mean for me".

The how?
Due to the nature of the case and Optus collaborating with the local, state and federal police, the specific details on how the breach occurred cannot be disclosed to the public. But here’s what we know.
The Australian Federal Police is looking into the origins of the Optus cyberattack and the methods used by the hackers. Optus has also commissioned a separate Deloitte investigation to uncover what happened and why.
Described as a “sophisticated” breech, the rumoured culprits engaged multiple European IP addresses that kept changing during the hack. In which the home affairs minister Clare O’Neil asserts the attack was “basic”.
She has criticised Optus for leaving its systems vulnerable through an unprotected Application Programming Interface (API), a computer program that allows software systems to talk to each other.
What was stolen? And from whom?
The Optus breach exposed over 10,000 individuals’ data, including 3,200 driver’s licenses, 151 overseas passports, and 37,000 Medicare numbers. It impacted customers from 2017, with potential effects on 9.8 million Australians, 2.8 million severely. Optus notified most affected customers but hasn’t informed some deemed less impacted.
How can you protect your data?
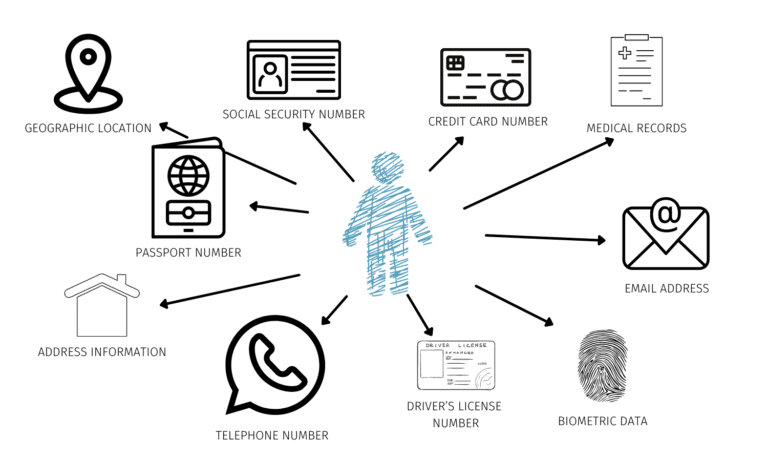
Securing passwords and personal data is crucial for businesses and individuals. Beyond traditional PII like credit cards, the evolving internet era deems even seemingly innocuous data, like email and browsing history, as personal. In the information society, redefining PII is vital for collective data protection.
Here are a few tips on how to keep your PII private and secure:
- Use Secure Passwords – Protect your passwords: mix upper/lowercase, numbers, symbols. Avoid easily guessed info like names, birthdays, addresses. Use strong, unique combinations.
- Share personal information with caution – This tip applies to both the online and offline worlds: Questions to ask yourself before sharing anything include:
- Who is asking for your personal information
- Why do they need it?
- How will they use it?
- What security measures do they have in place to ensure that your private information remains private?
- How to share information carefully – Share passwords cautiously for practical needs. Change them after tasks. Verify ongoing requests for shared access. Grant selectively.
- Don’t use the same password – Use a password manager to avoid using the same password across multiple accounts. Remembering many passwords is challenging without assistance.
- Avoid using personal platforms to send sensitive data – Using easily accessible platforms such as Email, messenger, or even WhatsApp can be a convenient way to send information quickly. Still, it’s impossible to ensure the intended recipient is the person who receives the document on the other end.
- Shred old documents and statements – Dispose of credit card and bank statements safely. Online access diminishes the need for printed statements, but shred documents to prevent identity theft. Thieves exploit seemingly insignificant details.
- Get rid of old data you no longer need – Keeping your computer and mobile devices clean is a good practice to ensure usability, but it’s also wise to eliminate old information you no longer need. Keep only the data you need for current routine business, safely archive or destroy older data, and remove it from all computers and other devices, including
- smart phones
- laptops
- external hard drives
Protecting your customer's data, protecting your business.
Protecting your personal and professional information online and on mobile is no different than protecting your house and personal assets. Security can be as simple as locking the doors or as elaborate as monitoring and alarm systems. The first step is a mindset that identifies the exposure, risk and management of your information whenever it’s requested.
Scantek is ISO 27001 Information Security Management compliant. Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It typically involves preventing the probability of unauthorised/inappropriate access to data.
Scantek is an Australian-owned and operated provider of cutting-edge ID verification software that is helping businesses improve efficiencies whilst safeguarding their customer’s personal and private information.
If you’re a manager or owner of a business seeking an Identity Verification solution widely used by organisations and local governments to improve data security, we welcome you to contact us to see how our technology can support your business.